If you’ve ever stumbled across a script labeled “8tshare6a” and asked yourself, “what is 8tshare6a python code”—you’re not alone. Countless developers, data enthusiasts, and curious minds are trying to figure out where it came from, what it does, and why it keeps appearing in random repositories or online forums. If you’re after clarity, take a look at this essential resource for a closer breakdown.
The Mysterious Origin of 8tshare6a
Before diving into specifics, let’s be clear: 8tshare6a isn’t a widely known package or library in the official Python ecosystem. It doesn’t originate from PyPI, GitHub, or any popular Python development hub. In most cases, when people ask what is 8tshare6a python code, they’re referring to a snippet or module found either in questionable repositories or bundled deep within scripts scraped from forums and online tutorials.
It first gained attention when developers found it embedded in scripts claiming to perform data extraction, API integrations, or even crypto wallet management. It didn’t take long for users to get suspicious, especially due to its obscure name and unpredictable behavior.
What the Code Typically Contains
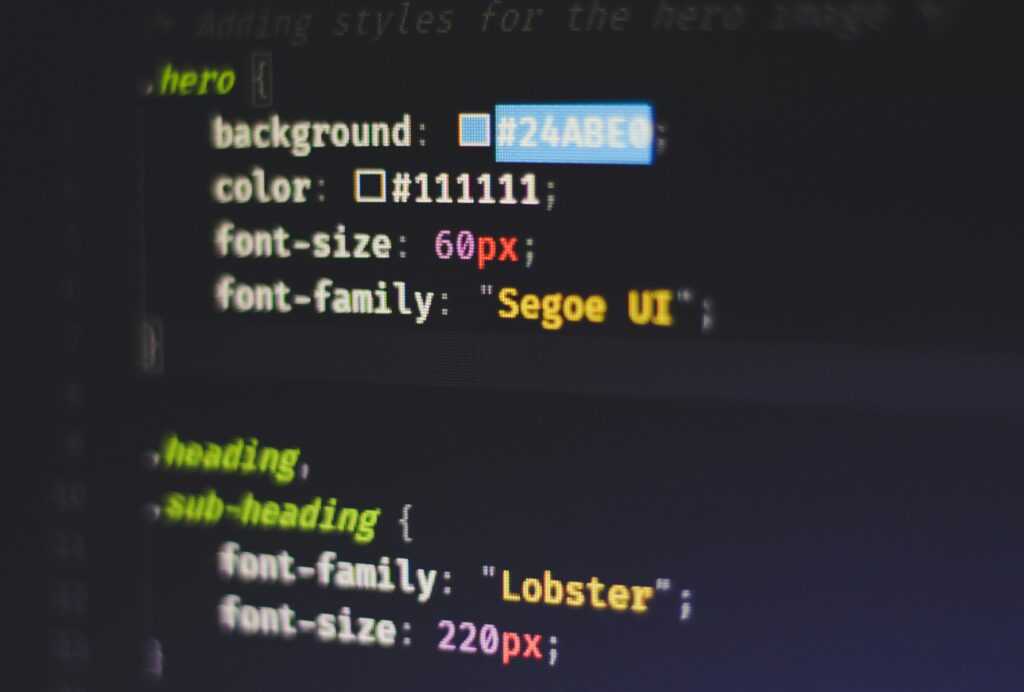
The actual content of 8tshare6a code varies—but there are some common themes:
- Obfuscated logic: Variables with meaningless names, minimal comments, and nested functions that make the code hard to read.
- Network activity: HTTP requests to unfamiliar or untrusted domains.
- File I/O operations: Writing temp files or logs, sometimes in hidden directories.
Depending on where it’s found, it might even include token-grabbing logic or behavior consistent with keyloggers—often buried under misleading function names like get_user_data() or connection_test().
So, for good reason, many people search for answers about what is 8tshare6a python code with heightened caution.
Why It’s a Red Flag (Most of the Time)
Let’s be candid: any Python code that doesn’t have documentation, behaves evasively, or connects to unknown servers is a risk—especially when it’s not from a vetted source. In the case of 8tshare6a, the red flags are:
- Zero official documentation
- No developer attribution
- Appears in bundled archives or copied/pasted snippets
Even worse, some versions of the code seem specifically crafted to bypass antivirus scans or hide their true function until deployed in a live system.
That doesn’t scream “harmless,” does it?
But Is It Always Malicious?
We’d love to give a binary answer, but tech rarely works that way. There’s no universal 8tshare6a.py file—they vary wildly depending on the source.
Some stripped-down variants are just shell scripts for automating IP checks, scraping Reddit data, or performing open-source intelligence (OSINT) tasks. These versions might be poorly executed, but not intentionally harmful.
Yet, that uncertainty is exactly why developers keep asking what is 8tshare6a python code. Without consistency and transparency, the code remains untrustworthy by default.
What To Do If You Find It
If you come across 8tshare6a code in your environment, treat it cautiously. Here’s a basic checklist:
- Inspect the code manually — Line by line, if possible.
- Google the exact hashes — Run a SHA256 hash of the file and search it.
- Use a sandbox — Load it into an isolated virtual environment and monitor its activity.
- Scan with security tools — Tools like VirusTotal or hybrid-analysis.com can catch known threats.
Don’t run it unless you’re sure of what it does. At the very least, you risk wasting system resources. At worst, you might compromise your environment.
Better Safe Than Curious
Sometimes curiosity pays off. Other times, it opens a backdoor to your system.
If you’re just trying to learn Python or automate basic tasks, there’s no reason to mess with something obscure and undocumented. Stick to trusted libraries, and avoid anything you can’t source or understand.
That said, if reverse-engineering shady code is your hobby or job—carry on, just make sure you’re properly sandboxed.
Closing Thoughts
To summarize, asking “what is 8tshare6a python code” is a legitimate question—and a fair warning signal. Most versions of this code aren’t helpful, structured, or transparent. Often, they raise more questions than answers. Unless it comes from a verified source and has well-documented functionality, it’s better left alone or handled with proper caution.
Still curious? This essential resource goes deeper into known patterns, sample scripts, and investigative notes that might help you trace its origins or function.